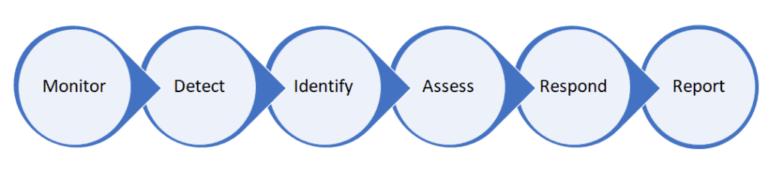
The SOC of T.net provides the automatic identification of threats, the response to incidents and the control of compliance (Article 32 of EU Regulation 679/2016), as well as providing information in the event of a Data Breach (Article 33 of EU Regulation 679/2016) adequate for notification to the Privacy Guarantor.
All this in a single unified solution! It also provides all the critical SOC capabilities needed for maximum security visibility in on-site and cloud environments. With T.net’s SOC service you can eliminate the need to manage multiple security elements and stop worrying about related management operations. The service allows you to be ready for safety audits in advance and always get real information on safety quickly, quickly and efficiently.
Our SOC detects new emerging threats and operates as an extension of your IT department, regularly analyzing the global threat environment and optimizing the rules on your security apparatus taking into account available information, including advanced rules for connecting client softwares, continuous updating of signatures for vulnerabilities, updating guidelines for your staff to always guarantee an adequate response and minimize attacks through “social engineering” and much more.
If your service requires it, our specialists will monitor the Dark and Deep Web to check in real time threats and / or data breaches towards your systems and / or your brand.
In addition, “simulated attacks” can be agreed to check the level of awareness of your staff and, moreover, the most appropriate answers and the best suggestions to ensure the security of your networks and services will come from our Threat Exchange and Unified Threat Management group.